The SolarWinds supply chain breach remains one of the most striking examples of top third-party risks being realized in recent history, exposing the information of some of the world’s most prominent companies and numerous high-profile government agencies.
It was not just the approximately 18,000 organizations, though, that were directly exposed, but countless business partners, service providers, suppliers, customers, and prospects that found themselves victims as well. In total, the breach cost victims an average of $12 million.
While already well known, the SolarWinds attack further exposed the fragility of a global economy that thrives on third-party relationships. These relationships help organizations improve performance and backfill talent and supply shortages, especially during the pandemic, but also broaden the attack surface for threat actors.
In a new study, “Third-Party Risk: A Turbulent Outlook,” Interos and the Cyber Risk Alliance surveyed more than 300 technology leaders to better understand how well organizations understand and manage top third-party risks.
What You’ll Find In The Third Party Risk Management White Paper
The survey highlighted the depth of third-party relationships and the need for improved risk management. On average, the majority of respondents (76%) contract with up to 25 different vendors, business partners, brokers, contractors, distributors, agents, and resellers. For large enterprises (companies with more than 10,000 employees), an astonishing 15% relied on more than 250 third-party providers.
Virtually all organizations (95%) indicated partnerships with IT software, platform, or service providers. This is not to say that these partnerships are bad – they enable today’s lightning-fast global delivery system.
Other key takeaways from the survey:
- 60% of respondents experienced an IT security incident in the past two years due to a third-party partner with access privileges. The most-likely consequences were the theft of sensitive data or a business outage.
- While 52% of those who experienced third-party related attacks indicated they lost less than $100,000 in damages, another 45% incurred higher costs, with a few paying $1 million or more.
- Victims impacted by the SolarWinds supply chain attack suffered everything from day-long shutdowns to crucial data leakages.
- Perhaps because of real or perceived threats from SolarWinds and similar top third-party risks, 70% of respondents ranked cyber the No. 1 or No. 2 risk among their third-party/supply chain partners.
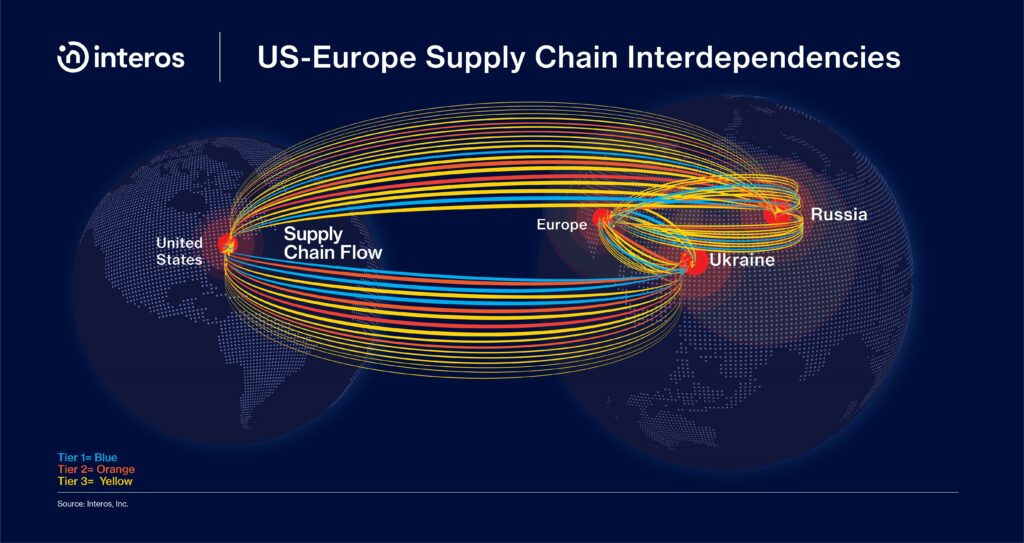
- Supply chain visibility is more essential than prior to the pandemic. Almost everyone wanted increased visibility, with 72% believing that tracking components, sub-assemblies, and final products was very or critically important.
- More than three out of four (76%) IT leaders and influencers rated managing third-party risk as a high or critical priority at their organizations — for most respondents (74%) this priority has increased in importance since 2020, when the pandemic created major micro and macro business disruptions, including supply and workforce shortages.
- Nearly half of all respondents (45%) said they implement the guidelines within the NIST Cybersecurity Framework in their third-party vendor assessments.
Third-Party Cyber Risk Management Has Never Been More Important
The survey found that the vast majority of respondents (72%) called supply chain visibility important, but only a small fraction actually had adequate insight into their suppliers.
In reporting their highest level of supply chain visibility, 41% had visibility only on their most critical third–party direct dependencies, while 26% could see the full map of interdependencies across all tiers in their supply chains.
The Covid-19 pandemic was regularly shared as a reason for lowered visibility. When asked about specific challenges in managing third-party risk, the top answer was a lack of qualified staff to implement a management solution (30%) and the ability to accurately assess and manage a large number of partners (26%).
To better manage top third-party risks, Interos advises companies to prioritize risk management and follow industry standards and guidelines such as the NIST Cybersecurity Framework. They should also adopt multiple methods to vet third-party providers, and continually reassess third parties for risk, among other solutions highlighted in the report. For more information about how Interos platform can help to assess and address these risks, visit interos.ai.